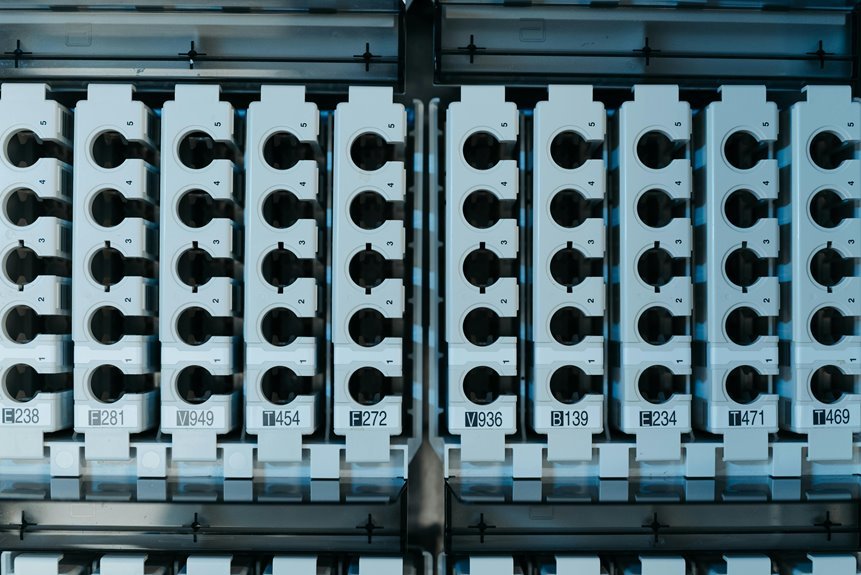
Technical Key Register for 934452768, 662912689, 8002002116, 919940036, 1513293786, 615805321
The Technical Key Register for the specified keys serves as a vital tool for managing sensitive information within the organization. It systematically documents access, enhancing accountability and reducing unauthorized risks. This process is not merely administrative; it plays a crucial role in maintaining security integrity. Understanding the implications of key management practices raises important questions about efficiency and security culture. What measures are necessary to further safeguard these critical assets?
Overview of Technical Keys
Technical keys serve as essential components in various systems, facilitating secure access and data protection.
Key classification ensures that different types of keys are organized based on their security levels and intended uses.
Effective key security measures protect these classifications, reducing the risk of unauthorized access.
Understanding these principles is vital for maintaining freedom in digital environments while safeguarding sensitive information from potential threats.
Functionality and Applications
Keys play a pivotal role in the functionality and applications of security systems across various industries. They ensure key security by safeguarding access to sensitive information and physical spaces.
Through application integration, these keys facilitate seamless communication between different systems, enhancing operational efficiency. Ultimately, their effective implementation allows organizations to maintain robust security while promoting a sense of freedom and autonomy in their operations.
Importance of Maintaining a Technical Key Register
Maintaining a technical key register is vital for organizations seeking to uphold their security frameworks. This practice enhances security measures by providing a systematic approach to managing sensitive keys.
Moreover, it ensures data integrity, minimizing the risk of unauthorized access or data breaches. A well-maintained register serves as a cornerstone for effective operational security, promoting both accountability and transparency within the organization.
Best Practices for Key Management
Effective key management is essential for safeguarding sensitive information within any organization.
Best practices include implementing strong key security measures, such as encryption and regular audits. Access control should be strictly enforced, ensuring only authorized personnel can manage keys.
Additionally, organizations must establish a clear key lifecycle policy to maintain accountability and minimize risks associated with key compromise or loss.
Conclusion
In conclusion, the Technical Key Register not only safeguards sensitive information through meticulous documentation of keys like 934452768 and 662912689, but it also coincidentally fosters a culture of security awareness among personnel. As organizations increasingly rely on digital security, the interplay between robust key management and operational efficiency becomes paramount. By adhering to best practices, organizations can navigate the complexities of security, ensuring that both accountability and access control work hand in hand to protect valuable assets.




